What Went Wrong—and How to Prevent It
A routine call to United Airlines customer service after a flight cancellation turned into a nightmare for Denver passenger Dan Smoker—who ended up losing $17,000 to a scammer posing as a United-affiliated agent. What exactly went wrong, and how can airlines and call centers avoid similar catastrophes?
The Scam Unfolded—Here’s What Happened
- Smoker’s flight to Europe was canceled due to a mechanical issue. He called United’s official customer service number to rebook with a Lufthansa codeshare partner. (Consumer Rescue, The Sun, ABC News)
- He was connected to someone identifying as “David,” who claimed to be a United associate. After being told he’d receive a refund, Smoker was directed to pay for new tickets via a suspicious link. (ABC News)
- Smoker later noticed discrepancies in the confirmation and credit card charge (“AIRLINEFARE,” not United), and attempts to contact “David” failed, revealing it was a scam. (ABC News)
- United confirmed the call was transferred outside their validated system—meaning the agent bypassed authentication tools. (9News)
Likely Causes: How the Scam Slipped Through
- Agent bypassed official systems
United reported that the agent transferred Smoker’s call to an external line without validating it, violating security protocols. (9News) - Potential call interception or spoofing
Some victims have reported being connected to scammers even after dialing a legitimate number—possibly due to techniques like call redirection or phone line hijacking. (Aviation A2Z, CX Today)
The mismatch between Smoker’s phone call duration (over three hours) and United’s recorded 12 minutes adds to the suspicion. - High-stress vulnerability
Travelers facing cancellations or rebooking often feel pressured and anxious—prime conditions for social engineering-based scams.
How Call Centers Can Block the Scam Track
1. Strict validation for external transfers
- Mandate agents to verify any transfer number against an internal whitelist or official directories before connecting calls to external parties.
2. Real-time monitoring of transfer frequency
- Security teams should flag unusual transfer patterns—especially for high-risk domains like rebooking or international routes.
3. AI-based detection tools
- Deploy systems that analyze call routing and detect anomalies (e.g., long call time not aligned with company logs).
4. Frequent agent training
- Keep agents updated about vishing (voice phishing), external impersonation tactics, and importance of verifying transfer targets.
5. Post-call auditing
- Regular audits of recorded calls and transfer logs can help catch suspicious incidents retrospectively and inform prevention strategies.
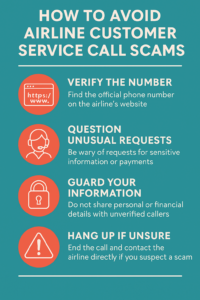
How Passengers Can Stay Safe
- Always try to solve issues through the airline’s official app or website before calling.
- Stick to trusted numbers—found on the airline’s site or your confirmation email—not those surfaced via search results.
- Watch for red flags: vague refund promises, odd URLs, or vague language.
- Verify payment links: official ones usually originate from secure company domains and come with consistent branding.
Broader Context: Vishing Gets Slicker
This isn’t an isolated case. According to the AARP, impersonation is a growing trend among scammers targeting travelers. They often mimic airline support to gain personal details or payments. (The Sun, Consumer Advice, Aviation A2Z)
Phone scams are evolving—particularly through vishing, where scammers may even spoof Caller ID or hijack legitimate calls via VoIP technology. (Wikipedia)
This case is a stark example of how trust in the system can be exploited, especially when callers are already in crisis mode after a flight cancellation. Investing in smart internal controls—paired with public awareness—can prevent both airlines and travelers from taking flights to fraud.